A substitution cipher is a method of encoding where each letter in the plaintext is replaced with a corresponding letter in the ciphertext. The key to decrypting the message is knowing which letters have been substituted for which. This type of cipher relies on a fixed system, which makes it relatively easy to understand but can be quite secure if implemented correctly.
How Does a Substitution Cipher Work?
The simplest form of a substitution cipher is the Caesar Cipher, named after Julius Caesar, who used it to communicate with his generals. In a Caesar Cipher, each letter in the plaintext is shifted a certain number of places down or up the alphabet. For example
- Plaintext: HELLO
- Ciphertext: KHOOR
Here, each letter has been shifted three places to the right. “H” becomes “K”, “E” becomes “H”, and so on.
Types of Substitution Ciphers
1. Simple Substitution Cipher: In this type, each letter of the plaintext is replaced with a unique letter of the ciphertext alphabet. Unlike the Caesar Cipher, the substitution is more complex and does not involve a uniform shift.
2. Polyalphabetic Cipher: This type uses multiple substitution alphabets to encrypt the plaintext. One of the most famous polyalphabetic ciphers is the Vigenère Cipher, which uses a keyword to shift letters differently at various points in the message.
For example, using the keyword “KEY”:
- Plaintext: HELLO
- Keyword: KEYKE
- Ciphertext: RIJVS
Here, “H” is shifted by K, “E” by E, and so on.
3. Homophonic Substitution Cipher: In this method, a single plaintext letter can be replaced by multiple possible ciphertext symbols. This adds an additional layer of security by making frequency analysis more difficult.
Historical Context
Substitution ciphers have a rich history. Julius Caesar used them for military communication, while Mary, Queen of Scots, used a simple substitution cipher in her plot to assassinate Queen Elizabeth I. Unfortunately for her, the cipher was broken, leading to her arrest and execution.
In the 20th century, substitution ciphers were a part of more complex encryption systems like the Enigma machine used by the Germans during World War II. The breaking of the Enigma cipher by Allied cryptanalysts was a turning point in the war.
Modern Uses
Today, while simple substitution ciphers are not secure enough for modern encryption needs, they are still used for educational purposes and in various puzzle games. They help students and enthusiasts understand the basics of encryption and cryptanalysis.
Cryptoquip and Cryptoquote are types of substitution ciphers. You can see the Cryptoquip answer today and the Cryptoquote answer today for both puzzles and their solutions.
Breaking a Substitution Cipher
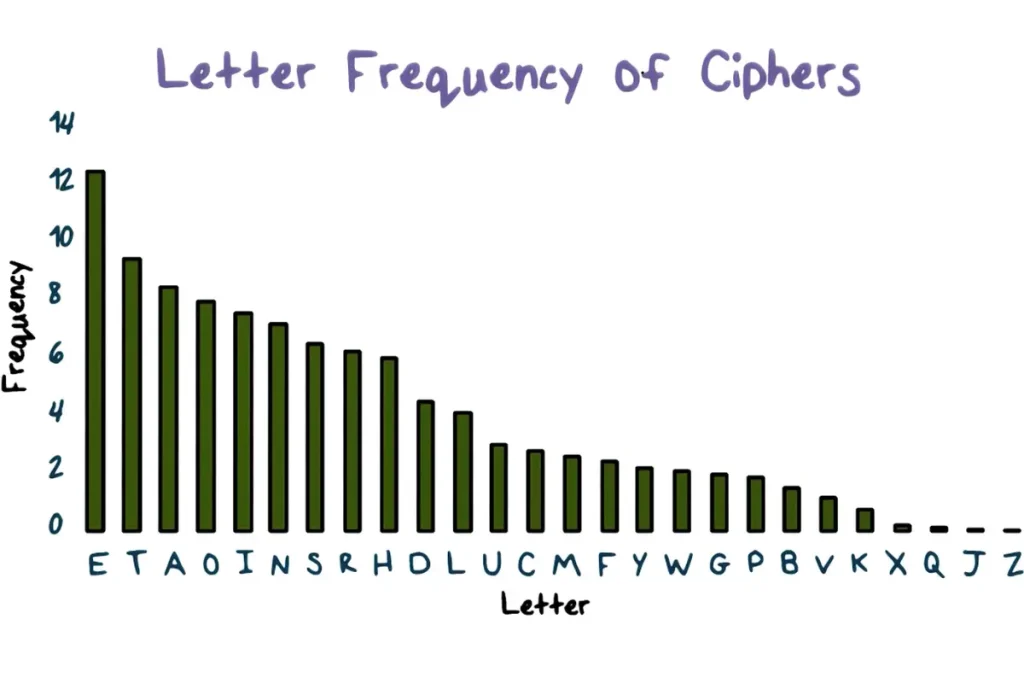
Despite their apparent simplicity, breaking a substitution cipher without knowing the key can be challenging. Cryptanalysts use various techniques, such as frequency analysis, to decipher messages. For example, in English, the most common letters are E, T, A, O, I, and N. By analyzing the frequency of letters in the ciphertext and comparing them to the known frequencies in the English language, one can start making educated guesses about the substitutions.